Wipe, Track, Lock & Dock: Securing Phones and Tablets
When deciding what tablets or smart phones to buy for your field service business, and where to buy them, how will you secure them against data breaches and unauthorized use?
May 11, 2015
# of Minutes to Read

When deciding what tablets or smart phones to buy for your field service business, and where to buy them, you will certainly consider durability, battery life, and the device’s ability to run your business software.
It is equally important, however, to consider how and under what circumstances you will be able to disable a device or restrict its use. A loss of customer or company data or inappropriate use of the device could be very expensive. If you have any doubts, check with your insurance agent!
Prevent unauthorized access with strong passwords
The first line of defense against unauthorized access to customer and company data is a password lock. Require employees to use strong passwords. Some devices allow you to set the lock to be opened with a swipe or pattern, but a strong password (using a combination of upper- and lower-case numerals and letter) is best.
Prepare to wipe a lost or stolen phone
If a device is lost or stolen, or an employee is terminated, you need to be able to remotely wipe data from the phone or tablet’s internal storage. Setup this function before sending the device into the field. Android’s Remote Wipe lets you wipe out a company profile without affecting personal data. iOS Find My iPhone will not only erase your device, but help you locate it and display a message asking a finder to contact you.
Implement a clear company policy on use
Non-business uses of a corporate device can distract employees from their work and open the door to data theft and malicious software.
Your first line of defense against misuse, infections or data breaches is a clear, reasonable company policy on mobile and Internet use. Take the time to present it and discuss it. Let your employees know you are serious about what sites they can access and whether and exactly what your expectations are regarding use of a corporate device for personal communication or other tasks.
Use technology to dedicate a device or restrict its use
Next, ask your mobile device supplier about settings and programs that restrict certain functions to administrators. Prevent unauthorized use and protect your system and customer and corporate data by restricting the following:
- Access to app stores (a potential source of malicious software).
- Data downloads from the device.
- Screen captures and copy-paste features.
- Access to Gmail, Yahoo and other personal email accounts.
- Access to Twitter, SnapChat, Facebook and other social media.
- Access to Internet browsers.
Lock out texting—or any phone use—while driving
Most state laws and any well-designed corporate technology policy ban texting while driving, and some ban any handheld phone use. If, however, it can be shown that your employees are implicitly encouraged to communicate with the office while driving, you may still be held liable for hefty damages in the event of a crash.
Technology can help reinforce your driving policy. There is a device on the market, Dock-n-Lock, that requires a mobile phone to be docked out of site while the vehicle is in operation, automatically forwarding calls to voice messaging. Apple CarPlay integrates Siri with a vehicle’s built-in display, allowing voice control of messaging. And look down the road for an Apple application that automatically shuts off certain functions when the user is driving (as identified by GPS and motion sensors).
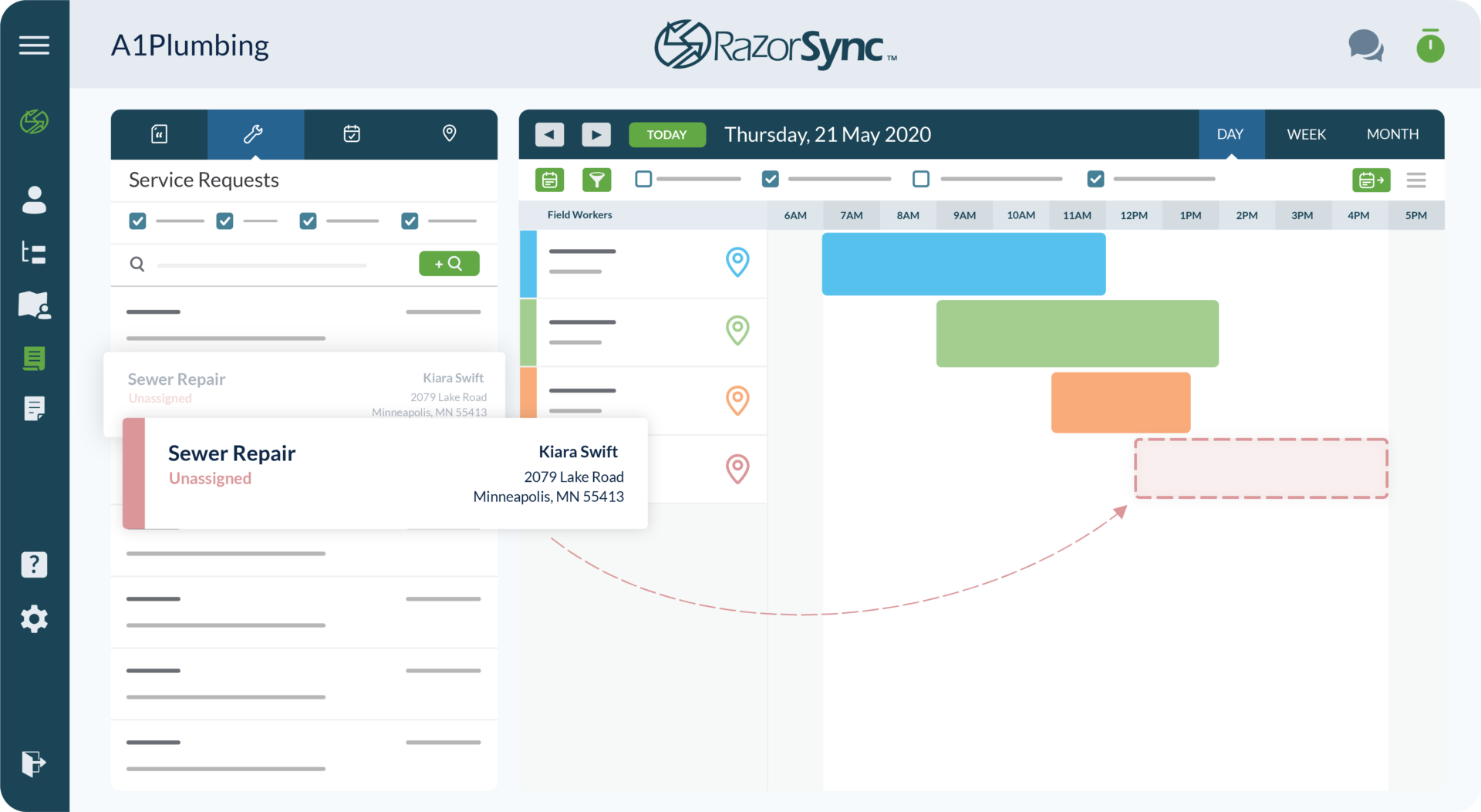
Protect and Enhance Your Field Service Business with Technology
RazorSync is committed to helping our customers optimize business opportunities in the safest, most economical way possible. Join a live demonstration or start a free trial to learn whether it is the right solution for you.