How Can You Protect Your Information When Using Wireless Technology? Understanding Risks and Taking Steps to Stay Secure In The Field Service Industry
Recently, an increasing amount of businesses have transitioned to primarily digital interfaces, raising significant concerns about how to keep company and personal information secure. Field...
Sep 21, 2021
# of Minutes to Read

Recently, an increasing amount of businesses have transitioned to primarily digital interfaces, raising significant concerns about how to keep company and personal information secure. Field service companies handle a great deal of private information for customers and should be asking: how can you protect your information when using wireless technology? To avoid security breaches and ensure data is protected, field service companies and technicians need to familiarize themselves with the potential risks of wireless technology and how to mitigate them.
Risks of Using Wireless Technology
Three general risks are associated with using wireless technology: intrusion, leeching, and exploitation. This can include personal information being found and stolen, bandwidth use by unwanted parties, and sharing illegal materials over a network.
- Intrusion is unwanted action on a digital network. If unauthorized users enter your network, they can steal private information. With access to data like passwords, credit cards, worker’s personal information, and more, a hacker can destroy a business.
- Leeching occurs when bandwidth is used by unwelcome parties outside of the company. Bandwidth refers to the amount of data that users can send at a specific time. When hackers take up bandwidth, business processes slow down significantly.
- Exploitation happens when people send illegal files over a network or attack other networks to slow them down or steal their data.
With many people working from home, there are a few specific examples that fall under these risk categories, including piggybacking, tailgating and evil twin attacks.
- Piggybacking happens when people within range of your wireless connection use your network, enabling them to access your files, search history, and other private information.
- Tailgating occurs when someone who should not have access to vaults of information gets admission without proper approval.
- Evil twin attacks happen when a person intentionally mimics a public network but offers a stronger network connection. Impatient, naive users looking for a quick connection will readily switch to what appears to be a secure, faster network. Unfortunately, the person who created the alternate system can then easily access user information. Passwords, card numbers, and any other personal data can be stolen and used.
By being aware of potential risks associated with wireless technology, issues can be avoided in the long run. For this reason, field service companies should remain vigilant and take steps to protect their networks.
Ways To Stay Secure
With the most common risks laid out above, the question is, how can you protect your information when using wireless technology? Luckily, keeping field service data secure in a digital environment is possible!
Here are a few tips on how to protect your field service company’s data:
Secure company Wi-Fi and network
Hackers and those with malicious intentions can easily guess a simple router default password. Once they bypass it, locating and stealing company information is all too easy. Instead, create a long, strong Wi-Fi password with many symbols and special characters to prevent Wi-Fi bypasses. A strong password might look something like this: E62!ml$Qb9k. With the variety of characters and lack of meaning, it would be difficult to guess.
You may be thinking to yourself, “How would I even memorize a password like that?” Well, you don’t have to. One method to keep your strong passwords secure but readily accessible is to use a tool like LastPass. This service stores encrypted passwords and allow you to restrict access to specific vaults of login information within the platform. This feature, for example, enables office staff to have access to different platforms than field technicians do.
The last step to securing your wireless router is to enable its network encryption for an additional layer of protection to ensure your valuable company data is safe.
Limit network access
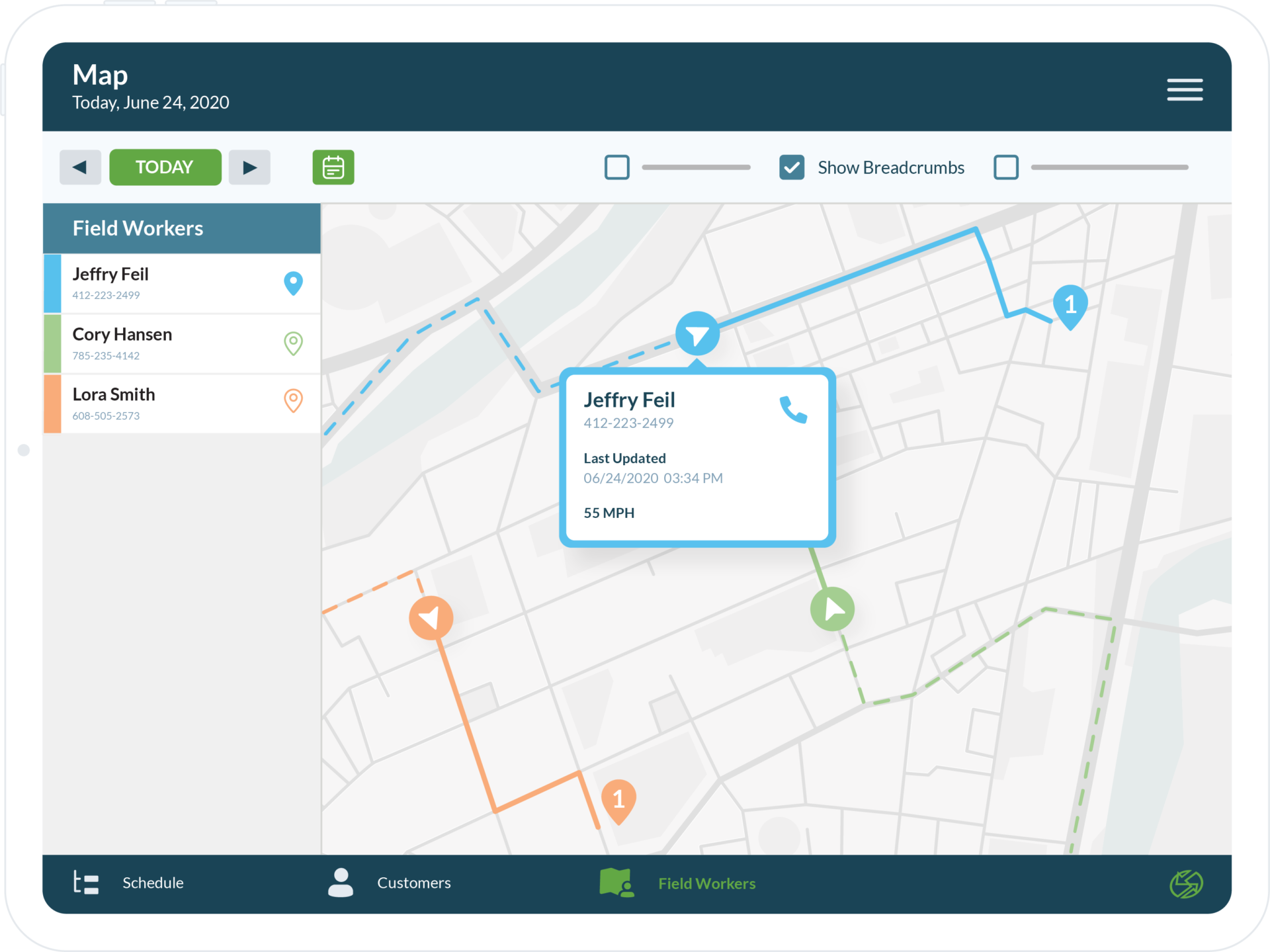
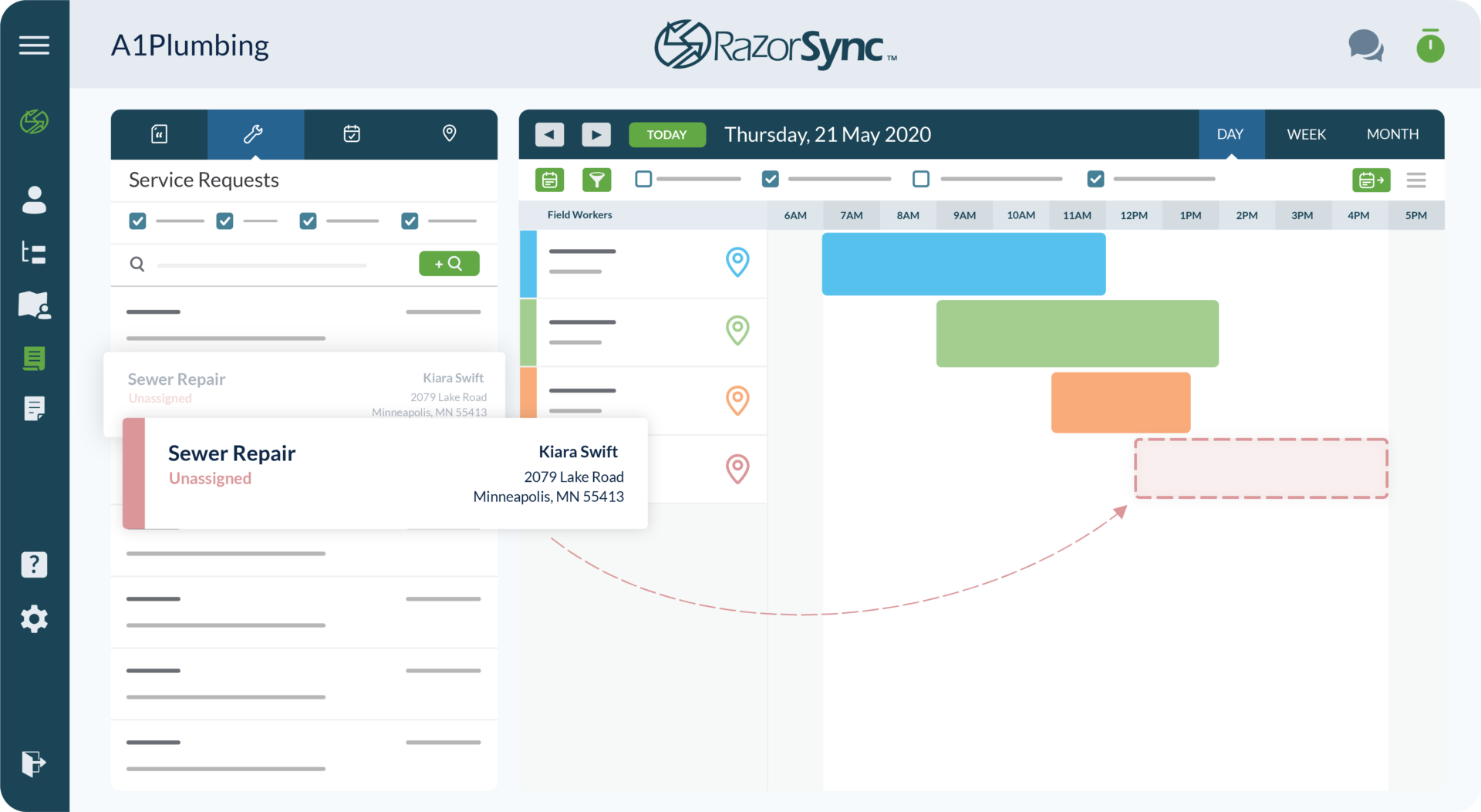
Only trusted field service company employees should have the ability to enter secure vaults and access private company information. Even then, restrictions should be placed on them to ensure a sufficient level of security. Establish strong security measures that deny restricted devices. This includes putting strong passwords on your Wi-Fi network and establishing a policy that company employees only conduct business operations on their work devices. By doing so, you’ll significantly lower the risk of unwanted intrusions such as piggybacking and tailgating.
Only share company information over private networks
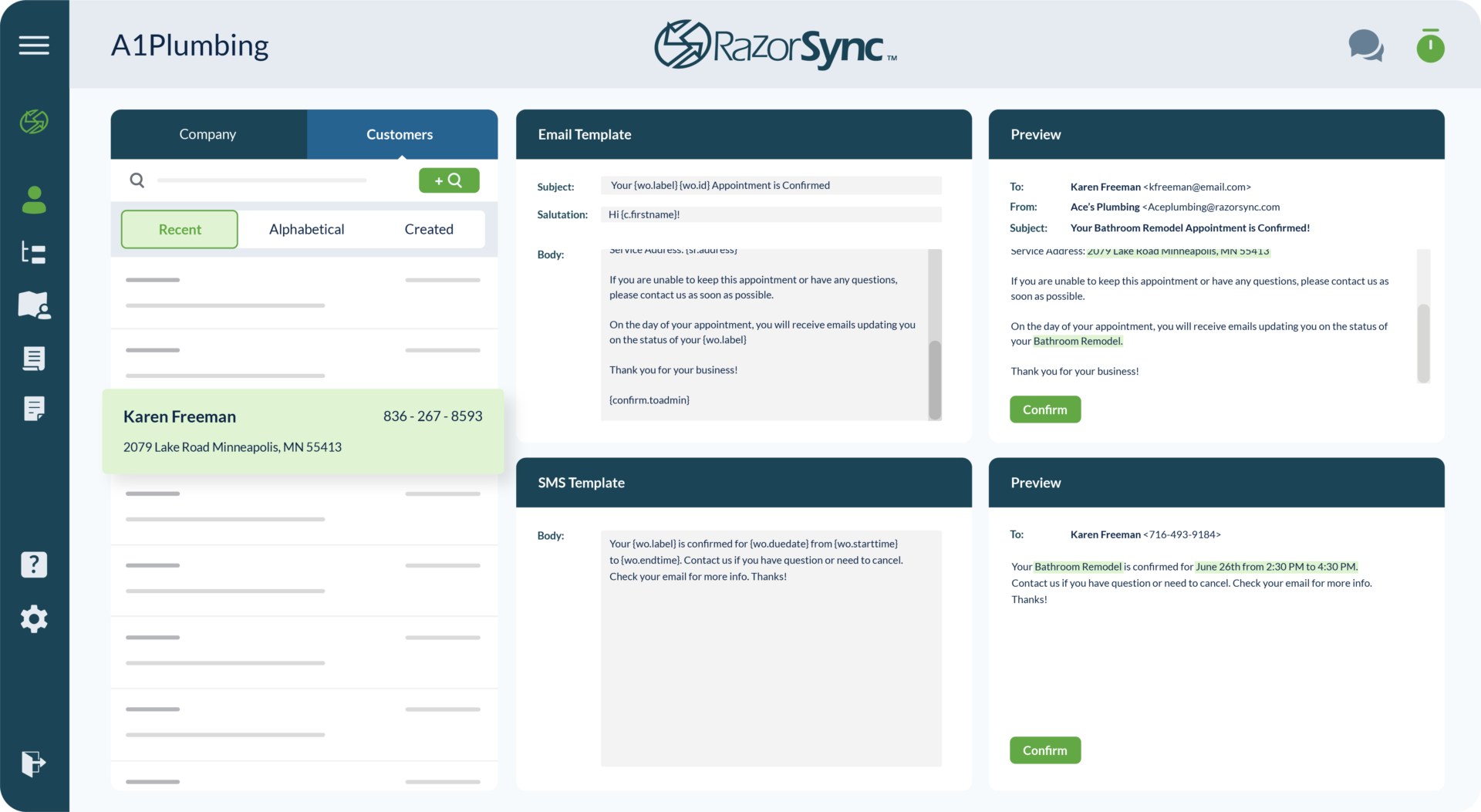
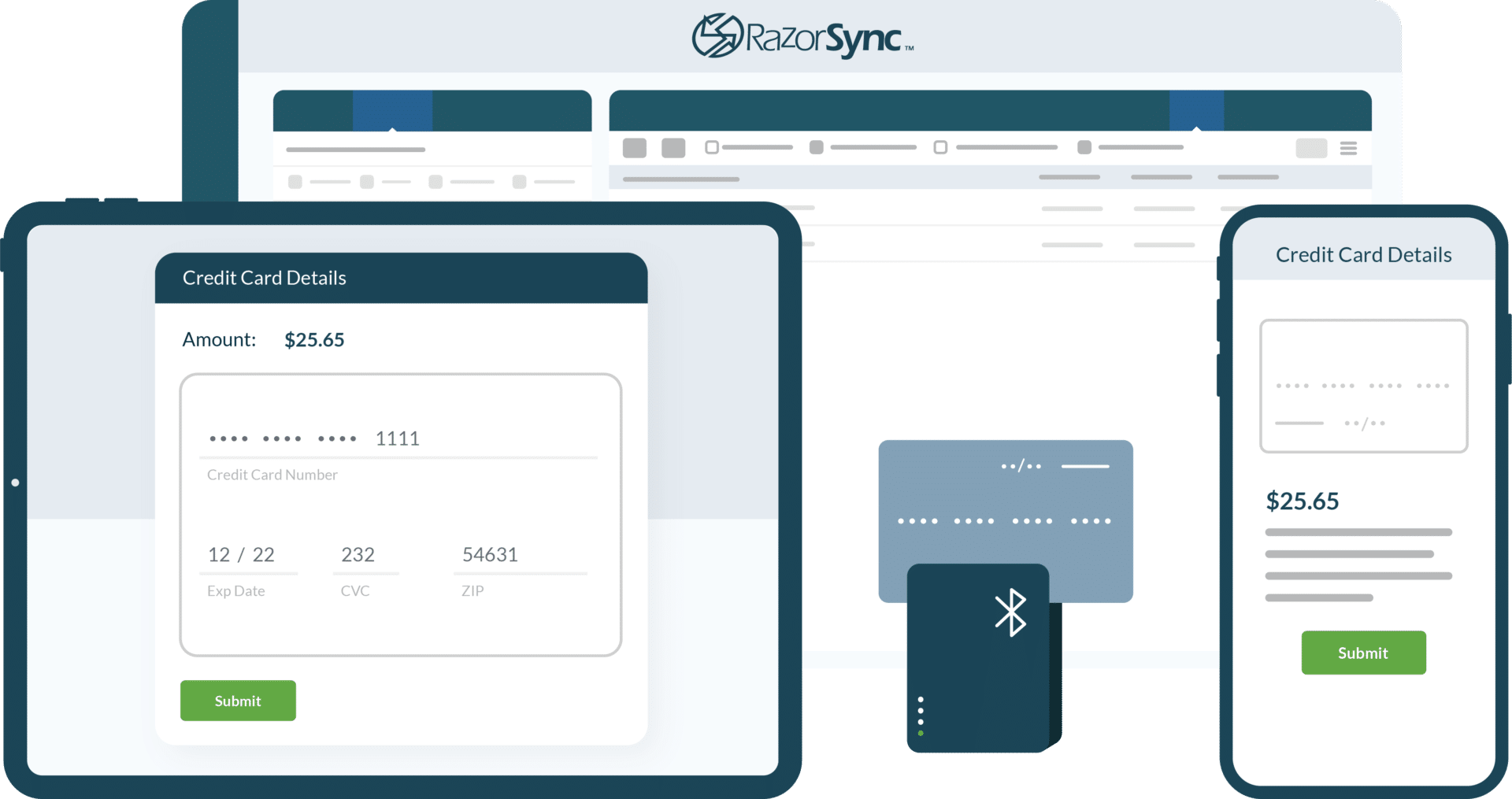
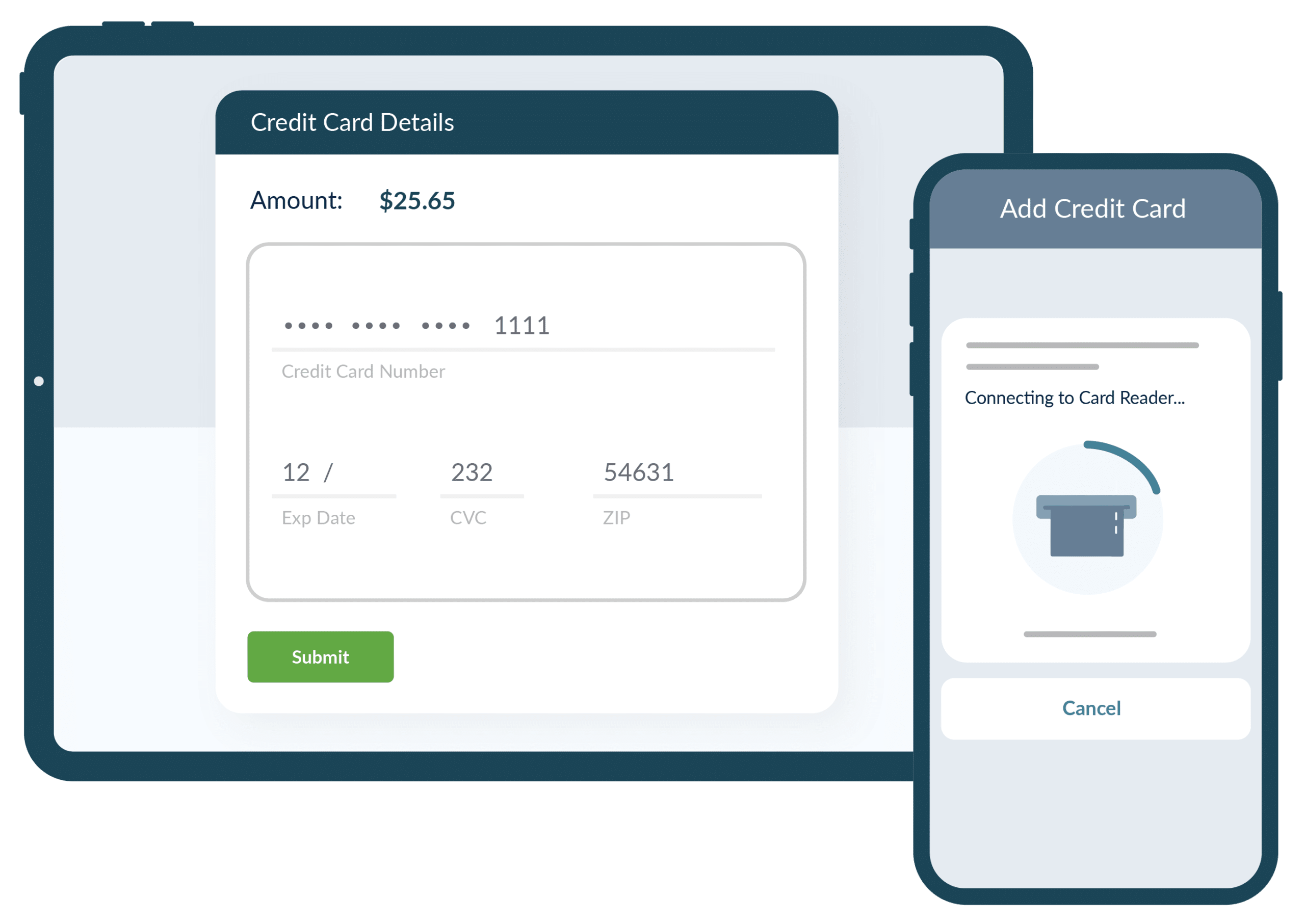
Field service companies are responsible for keeping their clients’ personal information secure, including credit card numbers and home addresses. The safest option to protect customers and secure their information is to transmit these messages over a private server dedicated to your business.
While obtaining your own server is an option (depending on the amount of bandwidth and memory, servers can cost anywhere from $100-$200 per month), a much easier solution for small businesses is a cloud platform, which allows you to skip the physical server entirely. With a serverless platform like Amazon Web Services (AWS), you’ll gain additional features and services, and there may even be free plans that may suit your company’s needs. Cloud computing and storage will also allow your business to remain agile, flexible, and secure.
With increased awareness of the risks of wireless technology and ways to mitigate them, you can start securing your networks right away. Remember that hackers have many ways to infiltrate your network, so being proactive about creating a secure environment is critical. Ensure you secure your company’s wireless networks by creating strong passwords and tracking all network users and their devices to protect company information.
You’re unlikely to regret taking the time to install these security measures, but you will certainly regret it if you don’t and suffer a data breach.